Resilience Testing Phishing
Resilience Testing Phishing evaluates an organization’s vulnerability to phishing attacks by simulating real-world phishing threats. Unlike Awareness Training, these tests do not immediately inform employees if they have fallen for phishing attempts. Instead, credentials are logged (if permitted) and risk exposure is assessed to identify weak points in security defenses. This approach provides an accurate measurement of an organization’s phishing resilience.

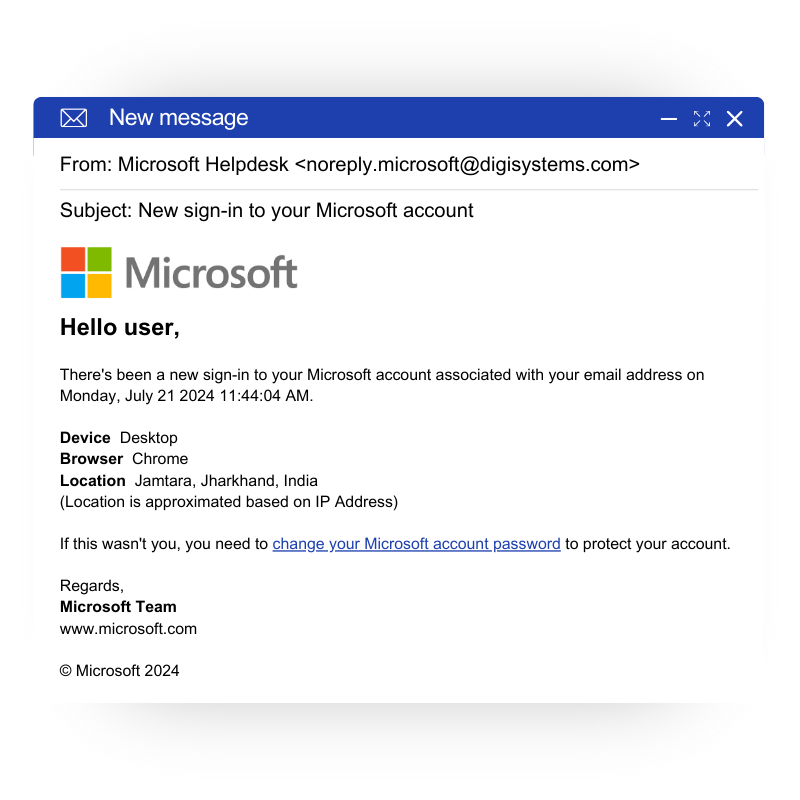
Phishing is a type of social engineering attack often used to steal user data, including login credentials and credit card numbers.
Trusted by
Resilience Testing Phishing Tiers
Resilience Testing Phishing content can be divided into different tiers that take into account the testing objectives and cybersecurity maturity of the organization, encouraging a budget-friendly and maturity-applicable testing approach.
Generic Phishing Testing
Standardized phishing emails are sent to all staff without warning.

Whitebox Phishing
Customized spear-phishing with provided internal data.

Greybox Phishing
Realistic phishing campaigns with public and internal data.

Blackbox Phishing
Bespoke campaigns through OSINT targeting high-value individuals.
How We Work?
Custom E-mails
Creation of customized e-mails with the help of our experts for the highest level of realism, undetectability and immersion
Randomized Sending
E-mails are sent at randomized intervals to reduce detection and avoid creating patterns
Detailed Tracking & Monitoring
GoPhish offers real-time tracking and monitoring of the campaign in terms of success – clicks, opens, submissions and more
Comprehensive Reporting
Each phishing campaign comes with an analytic report of the progress of the campaign as well as key findings and vulnerabilities
GoPhish
RiskSight’s Phishing Campaigns are carried out on a powerful and widely recognized open-source software called GoPhish. Hosted on RiskSight’s servers and operated only by authorized specialists, GoPhish allows for the quick and realistic creation and conduct of phishing simulations. The software is particularly noted for its robust analytical module, which provides comprehensive, real-time statistics on the campaign’s progress and success.

Technical Specifications




